Pharos Production collaborated with a taxi aggregator platform to develop a high-load ride-hailing application that connects passengers and drivers in real time. This platform consolidates various fleets and independent drivers into a single system, ensuring quick ride matching, live tracking and transparent pricing. Built on a cloud-native infrastructure, the solution offers low-latency interactions, reliable trip processing and scalability for operations at the city and regional levels.
Reviewed by Dr. Dmytro Nasyrov, Founder and CTO • Last updated April 30, 2026 • Editorial policy
Security Services
- 90+ engineers
- 18 industries
- 13+ years in business
What is security and QA in software development?
- Compliance certification issuance - we assess and prepare, certified bodies issue
- Bug bounty program operation - we perform structured assessments, bounties run on platforms like HackerOne
- Incident response retainers without prior assessment baseline
- Audits where the client is unwilling to share source code
Independent security audit vs internal AppSec team: which is better?
Independent audits give you a fresh adversarial perspective and a defensible report for customers and regulators, while internal AppSec teams give you continuous coverage and tribal knowledge. According to NIST Cybersecurity Framework 2.0 guidance, the strongest security postures use both: a continuous internal team plus periodic independent audits at major releases and compliance milestones.
| Factor | Independent audit | Internal AppSec only |
|---|---|---|
| Adversarial perspective | Fresh eyes; no assumptions baked in by the build team | Familiarity blindspots; harder to challenge own design |
| Defensible report | Third-party report for customers, regulators and insurers | Internal memo; less weight with external stakeholders |
| Coverage cadence | Periodic deep dives at major releases or compliance milestones | Continuous; integrated into PR review and CI |
| Tooling investment | Mature commercial tools shared across many engagements | Cost of building and maintaining your own tooling |
| Specialization | Smart contract / cloud / mobile / appsec specialists per engagement | Generalist coverage; deep specialization is expensive |
| Remediation support | Findings + concrete remediation guidance + retest pass | Owned by build team; varies by engineer skill |
| Cost (year 1) | $30,000-$120,000+ depending on scope and audit type | $200K-$500K loaded for 2-3 senior AppSec hires |
| When to use which | Pre-launch, post-major-release, compliance audits, customer due diligence | Continuous protection across day-to-day shipping |
Security and audits at Pharos Production at a glance
- Engagements: 50+ formal security engagements since 2018 with deliverable reports
- Smart contract audits: 100+ contracts audited and deployed to mainnet; zero critical vulnerabilities reported
- Tooling: Slither, Mythril, Foundry fuzzing, Echidna, Burp Suite Pro, ZAP, Semgrep, CodeQL, Tenable, Nessus
- Coverage: Smart contract audits, web/API pen tests, mobile pen tests, cloud config review, source code audits, threat modeling
- Pricing: Smart contract review from $8,000-$25,000; web/API pen test $12,000-$40,000; full security audit $30,000-$120,000+
- Timeline: Smart contract review 1-3 weeks; web pen test 2-4 weeks; full audit 4-8 weeks with remediation cycle
- Compliance support: SOC 2, ISO 27001, PCI DSS, HIPAA, GDPR readiness assessments. Not a certification body
- Honest scope: We recommend the right depth: a 1-day threat model often beats a $40K pen test for early-stage products
Selected security engineering projects we delivered
Our security practice runs threat models before any code, not security theater. A senior security engineering team with public disclosures and CVE credit, audit-grade tooling on every engagement and 50+ formal security engagements delivered since 2018 across smart contract audits, web and API pen tests, mobile assessments, cloud configuration review and source-code audits for FinTech, Web3, healthcare and SaaS clients. We work the full stack: threat modeling (STRIDE, PASTA, LINDDUN), secure SDLC integration (SAST, DAST, SCA gated against OWASP ASVS), manual and automated pen-testing with MITRE ATT&CK coverage, smart contract review under Foundry, Slither and Mythril, plus continuous monitoring under SIEM and EDR keyed to NIST CSF 2.0 Detect and Respond. We routinely advise clients to NOT invest in custom security tooling when proven managed-detection-and-response platforms (CrowdStrike, SentinelOne, Microsoft Defender XDR) win on cost, coverage and 24x7 staffing - and we say so before quoting. Below are selected security engineering projects delivered for regulated and high-value clients.
-
-
Pharos Production has partnered with Sagas to create a location-aware social platform that enables users to capture, publish, and explore geo-located timelapses over time. This system combines real-time data ingestion, large-scale media processing, and map-centric discovery to transform physical locations into dynamic digital stories. Leveraging cloud-native infrastructure and event-driven architecture, Sagas allows users to document urban changes, natural evolution, and personal moments tied to specific places. The result is a scalable social network where time and location are central to content discovery.
-
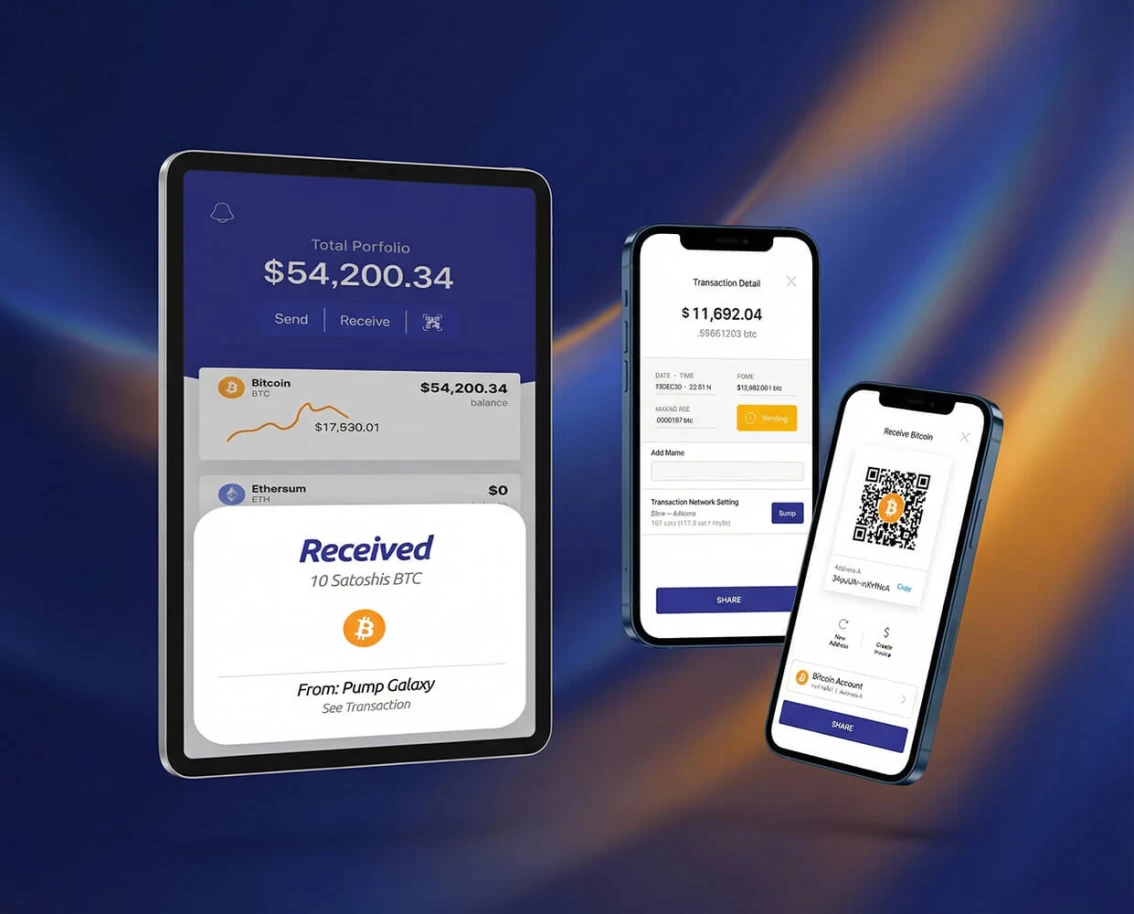
Pharos Production has partnered with PumpTap to develop a secure, high-performance crypto wallet tailored for everyday Web3 interactions. PumpTap lets users store, send and manage digital assets across multiple blockchains through a simple, intuitive interface. Built on a scalable, event-driven architecture, the wallet delivers real-time transaction updates, robust security and seamless integration with decentralized applications.
-
Pharos Production has partnered with Pulse to create a community-driven social network that connects users with local stores through challenges, engagement activities, and real-world prizes. This platform transforms everyday local interactions into interactive experiences, enabling users to earn rewards from participating merchants. Built on a scalable, event-driven architecture, Pulse facilitates real-time interactions between users and businesses and supports rapid growth across cities and regions.
-
Pharos Production partnered with Pro Gambling to build a high-load sports forecasting platform focused on data-driven predictions, real-time analytics and scalable delivery of betting insights. The platform aggregates large volumes of sports data, odds movements and historical statistics to generate forecasts that help users make informed betting decisions. Built on a cloud-native, event-driven architecture, Pro Gambling delivers fast updates, transparent analytics and consistent performance during peak sports events.
-
Pharos Production has partnered with Pleenk to build a secure, scalable payments platform for fast transactions, fraud prevention and seamless integration with digital products. The platform processes payment flows in real time while maintaining high levels of security, transparency and reliability for both businesses and end users. Built on cloud-native infrastructure and an event-driven architecture, Pleenk provides a strong foundation for modern digital payments.
-
Pharos Production partnered with NoMoreBets to develop a worldwide one-tap live betting platform focused on speed and scalability. The system handles real-time odds and instant bets effortlessly. The result is a smooth, engaging betting experience that increased player retention, reduced drop-offs during live matches, and positioned NoMoreBets for global growth since 2022.
-
Pharos Production partnered with Nextcheck to replace outdated, manual onboarding with a secure, automated KYC/AML platform. Built on AWS, Kubernetes, Istio, Elixir, RabbitMQ, PostgreSQL and NextJS, the platform provides real-time biometric and document verification, risk assessment and compliance reporting. Since 2019, Nextcheck has reduced onboarding time by 60%, cut manual labor by 70% and expanded to support thousands of checks at once. Today, it powers global banks, fintechs and crypto firms with a cloud-native, regulation-ready, growth-oriented compliance platform.
About Founder and CTO

Founder and CTO Pharos Production
I design and build reliable software solutions — from lightweight apps to high-load distributed systems and blockchain platforms.
PhD in Artificial Intelligence, MSc in Computer Science (with honors), MSc in Electronics & Precision Mechanics.
-
13 years in architecture of great software solutions tailored to customer needs for startups and enterprises
-
23 years of practical enterprise customized software production experience
-
Lecturer at the National Kyiv Polytechnic University
-
Doctor of Philosophy in Artificial Intelligence
-
Master’s degree in Computer Science, completed with excellence
-
Master’s degree in Electronics and precision mechanics engineering
Pharos Threat-Model-First Pipeline
The Pharos Threat-Model-First Pipeline is our four-step delivery cycle for security engagements: Threat Model and Asset Mapping, Secure SDLC Integration, Pen-Test and Red-Team, and Continuous Monitoring and Incident Response. Threat Model and Asset Mapping (1-2 weeks) inventories every asset, trust boundary and data flow then runs structured threat enumeration against STRIDE, PASTA and LINDDUN taxonomies aligned to the NIST Cybersecurity Framework 2.0 Identify and Protect functions - artifacts: asset inventory, attack tree, trust-boundary diagram, prioritised threat catalogue. Secure SDLC Integration (2-4 weeks) wires SAST, DAST and SCA into CI with policy-as-code gates against OWASP ASVS and CIS Controls v8 baselines, plus Semgrep, CodeQL, Dependabot, Trivy and gitleaks routed to engineer owners not a shared inbox - artifacts: pipeline config, control-mapping matrix, policy-as-code rules. Pen-Test and Red-Team (2-4 weeks) executes manual and automated assessment with attacker-technique coverage tracked against MITRE ATT&CK, scoped to the threat model from step 1 - artifacts: technical findings report, ATT&CK coverage matrix, executive risk summary, retest pass after remediation. Continuous Monitoring and Incident Response (ongoing) installs SIEM, EDR and detection content keyed to ATT&CK techniques, plus a documented runbook tested against FIRST.org incident-response standards - artifacts: detection rules, IR runbook, tabletop exercise log, post-incident review template. The pipeline is named because security is a lifecycle, not a one-shot audit - we re-enter Threat Model on every architectural change, new dependency or compliance audit cycle.
-
Phase 01 / 04 Paid Discovery
2-4 weeks- Technical validation
- Architecture proposal
- Scope refined estimate
-
Phase 02 / 04 Iterative Build
2-week sprints- Working demos every sprint
- CTO review at milestones
- ADRs documented
-
Phase 03 / 04 Production Readiness
- Monitoring and alerting
- Security audit Pen test
- Runbooks and rollback
-
Phase 04 / 04 Support
Ongoing- Security patches
- Performance tuning
- 4h SLA response
Pharos Verified Delivery applied to 70+ production applications since 2013
Real client transformations
Anonymized before/after snapshots from production projects. Metrics measured against client-reported pre-engagement baselines.
Pre-audit smart contract codebase contained 4 high-severity vulnerabilities found by Pharos before mainnet deployment. Reentrancy in withdrawal function would have allowed full drain.
All 4 vulnerabilities fixed during audit. Re-audit confirmed clean. Contract deployed to mainnet with $12 million TVL across 18 months without incident.
Reentrancy was caught by <a href="https://github.com/foundry-rs/foundry" target="_blank" rel="noopener nofollow">Foundry</a> invariant fuzz after 200M iterations surfaced an unexpected state transition. We reproduced the bug deterministically, delivered a 1-line fix (checks-effects-interactions), and added a permanent invariant test to the regression suite.
FinTech web app handled $40M monthly transaction volume. Internal security review found nothing. External pen test had not been performed.
Pharos pen test found 1 critical and 7 high-severity vulnerabilities including authentication bypass and IDOR. All fixed within 3 weeks. Subsequent quarterly tests find only minor issues.
The critical was a JWT verification bug that let an attacker escalate to admin with a crafted token; IDORs let authenticated users read adjacent account balances. Fixes shipped with a permanent authorization middleware pattern the client now reuses across all services.
Security testing was manual and ad-hoc. Vulnerabilities reached production. Each release required 2 weeks of manual security review.
Automated CI pipeline with SAST, dependency scanning and secrets detection. Vulnerabilities caught at PR time. Release security review reduced to 4 hours. Zero critical issues in production for 14 months.
Semgrep rules scoped to the client codebase, Dependabot with auto-PR remediation, gitleaks on every push, and a weekly Trivy scan of container images. Findings route directly to engineer owners via Slack instead of a shared security inbox.
Client names anonymized under NDA. Full case studies at /cases/.
When a full security audit is not the answer
We decline roughly 30% of RFPs we receive. Forcing a bad fit costs both sides 3-6 months and damages outcomes. Here is how we think about scope:
- Internal-only tools with no external attack surface
- Greenfield projects without an MVP to test
- Compliance "checkboxes" without budget to fix what you find
- Audits requested for marketing without intent to remediate
Not every project needs a full pen test. Sometimes a code review or SAST baseline is enough. Sometimes a threat model session catches issues before code is written. We start by understanding asset value and attacker motivation, then recommend the appropriate depth - not the most expensive option.
Read before you commit
100+ contracts audited and deployed to mainnet with zero critical vulnerabilities. Automated pipeline with Slither, Mythril and Foundry fuzz combined with manual expert review.
- A penetration test is a snapshot in time. New vulnerabilities can appear the day after the report is delivered through a new dependency CVE, a misconfigured deployment or a fresh attacker technique. Defense in depth plus continuous monitoring against the NIST Cybersecurity Framework 2.0 Detect and Respond functions is the practical posture, not a single annual audit.
- Pharos security engagements do not replace compliance attestation. SOC 2 reports are issued by AICPA-licensed CPA firms; PCI DSS reports of compliance are issued by PCI-SSC-registered QSA firms; ISO 27001 certificates are issued by accredited certification bodies. We perform readiness assessments, design controls and prepare evidence so the certification audit passes on first attempt - we are not the issuing body.
- Zero-day exploits cannot be prevented by audit alone. The mitigations that work are layered defenses, least-privilege architecture, segmentation, EDR and SIEM with detection content keyed to MITRE ATT&CK techniques and a tested incident-response runbook aligned with FIRST.org standards. Annual threat-landscape data from ENISA consistently shows zero-day and supply-chain exploits among the highest-impact attack categories.
- Cybersecurity insurance is now a baseline requirement for any system handling material customer data. Pharos does not place coverage. Clients must obtain cyber liability insurance from a licensed broker; we will provide the technical attestations carriers ask for during underwriting and renewal.
- Cross-border data residency obligations vary widely (EU GDPR, California CCPA, China PIPL, India DPDP, Brazil LGPD and emerging US state laws). Pharos engineers data-handling controls to client direction; the underlying privacy programme, lawful-basis selection and data-subject rights operations are the client legal responsibility. We will not deploy production systems handling regulated personal data without evidence that qualified privacy counsel has reviewed the data flows.
Reviews
Independent reviews from Clutch, GoodFirms and Google - verified client feedback on our software projects
Based on 8 verified client reviews
Platforms We Work With
Trusted by Coinbase, Consensys, Core Scientific, MicroStrategy, Gate.io and 10+ more Web3 and enterprise platforms
16+ partnersOur 16 technology partners include:
- Consensys
- Gate Io
- Coinbase
- Ludo
- Core Scientific
- Debut Infotech
- Axoni
- Alchemy
- Starkware
- Mara Holdings
- Microstrategy
- Nubank
- Okx
- Uniswap
- Riot
- Leeway Hertz
-
Consensys
-
Gate Io
-
Coinbase
-
Ludo
-
Core Scientific
-
Debut Infotech
-
Axoni
-
Alchemy
-
Starkware
-
Mara Holdings
-
Microstrategy
-
Nubank
-
Okx
-
Uniswap
-
Riot
-
Leeway Hertz

Reviewed by Dmytro Nasyrov
Founder and CTO
23+ years in custom software development. Led 70+ projects across FinTech, healthcare, Web3 and enterprise. aligned with ISO 27001 team.
Choose your cooperation model
Core software architecture, initial UI/UX, working prototype in 3 months
Software architecture, UI/UX, customized software development, manual and automated testing, cloud deployment
Comprehensive software architecture and documentation, UI/UX design layouts, UI kit, clickable prototypes, cloud deployment, continuous integration, as well as automated monitoring and notifications.
Prices vary based on project scope, complexity, timeline and requirements. Contact us for a personalized estimate.
Or select the appropriate interaction model
Request staff augmentation
Need extra hands on your software project? Our developers can jump in at any stage – from architecture to auditing – and integrate seamlessly with your team to fill any technical gaps.
Hire dedicated experts
Whether you’re building from scratch or scaling fast, our engineers are ready to step in. You stay in control, and we handle the code.
Outsource your project
From first line to final audit, we handle the entire development process. We will deliver secure, production-ready software, while you can focus on your business.
| Model | Best for | Team setup | Budget range |
|---|---|---|---|
| Staff Augmentation | Existing teams needing extra engineers at any project stage | 1-2 weeks | From $5,000/month |
| Dedicated Team Popular | Long-term projects requiring full ownership and control | 2-4 weeks | From $15,000/month |
| Project Outsourcing | Full-cycle development from idea to production launch | 1-2 weeks | $10,000-$80,000+ |
Technologies, tools and frameworks we use
Our engineers work with 187+ technologies across blockchain, backend, frontend, mobile and DevOps - chosen for production reliability and performance.
AI and Machine Learning
LLM Providers 8
AI Frameworks 15
Vector Databases 7
MLOps and Infrastructure 11
AI Agent Tools 4
Blockchains
Private and Public Blockchains 33
Cloud Blockchain Solutions 4
DevOps
DevOps Tools 15
Clouds
Clouds 6
Databases
Databases 15
Brokers
Event and Message Brokers 7
Tests
Test Automation Tools 6
UI/UX
UI/UX Design Tools 12
Partnerships & Awards
Recognized on Clutch, GoodFirms and The Manifest for software engineering excellence
An approach to the development cycle
-
Team Assembly
Our company starts and assembles an entire project specialists with the perfect blend of skills and experience to start the work.
-
MVP
We’ll design, build, and launch your MVP, ensuring it meets the core requirements of your software solution.
-
Production
We’ll create a complete software solution that is custom-made to meet your exact specifications.
-
Ongoing
Continuous Support
Our company will be right there with you, keeping your software solution running smoothly, fixing issues, and rolling out updates.
Frequently asked questions about security engineering
Type to filter questions and answers. Use Topic to narrow the list.
Showing all 7
No matches
Try a different keyword, change the topic, or clear filters
-
Pharos smart contract reviews start at $8,000 for a single contract, $25,000-$60,000 for a contract suite (lending, AMM, NFT marketplace, bridge). External audits from Trail of Bits, ConsenSys Diligence and OpenZeppelin typically run $40,000-$150,000+. We often deliver Pharos pre-audit pipelines that catch 80% of issues at 1/5 the cost so external audits pass on first round.
-
Smart contract review: 1-3 weeks. Web/API pen test: 2-4 weeks.
Mobile pen test: 2-3 weeks. Cloud configuration review: 1-2 weeks. Full source code audit with threat model: 4-8 weeks including a remediation review pass. Timelines depend on codebase size, complexity and how quickly the team can answer environment questions during scoping.
-
No - Pharos is not a certification body. Accredited auditors (AICPA-licensed CPAs for SOC 2, accredited firms for ISO 27001 and PCI SSC QSAs) issue the certificates. We perform readiness assessments, design control implementations, build evidence collection automation and walk you through the certification audit so you pass on first try. Pharos is itself aligned with ISO 27001, so we know the inside of the process.
-
Executive summary with risk-rated findings; full technical writeup per finding (impact, attack scenario, reproduction steps, remediation guidance, references); compensating controls where applicable; retest pass after remediation; defensible methodology section for auditors and regulators. Reports are written so engineers can fix issues immediately and so executives and customers can understand the risk posture.
-
We do incident triage and root cause analysis on smart contract exploits, web application breaches and cloud account compromises. We are NOT a 24×7 IR retainer or forensics firm; we do not handle law enforcement coordination, court-admissible chain-of-custody evidence or formal forensics.
For those, we partner with specialized IR firms and hand off when scope demands it.
-
Free 1-hour scoping call covering: target system architecture, deployed environments, authentication model, third-party dependencies, regulatory requirements, prior audit findings. Output is a fixed-fee statement of work with target findings categories, methodology, deliverables and timeline.
We never start work on a hourly-bill basis without an agreed scope.
-
We decline when: the requested depth is wrong for the asset value (e.g. $40K pen test on a pre-launch MVP); 24×7 IR retainer is needed (we are not staffed for it); the engagement requires regulator-issued certification (we are not a certification body); or the client wants a “compliance theater” report without actually fixing findings. Honest scope is part of how we run the practice.
Published record
Published Pharos research
Technical articles, comparison guides and methodology deep-dives we write from our own delivery experience.

Your business results matter
Achieve them with minimized risk through our bespoke innovation capabilities
What happens next?
-
Contact us
Contact us today to discuss your project. We’re ready to review your request promptly and guide you on the best next steps for collaboration
Same day -
NDA
We’re committed to keeping your information confidential, so we’ll sign a Non-Disclosure Agreement
1 day -
Plan the Goals
After we chat about your goals and needs, we’ll craft a comprehensive proposal detailing the project scope, team, timeline and budget
3-5 days -
Finalize the Details
Let’s connect on Google Meet to go through the proposal and confirm all the details together!
1-2 days -
Sign the Contract
As soon as the contract is signed, our dedicated team will jump into action on your project!
Same day
Our offices
Headquarters in Las Vegas, Nevada. Engineering office in Kyiv, Ukraine.